Encrypted data, multinational technology giants and the U.S. government. It all sounds very spy-chic, but the latest case revolving around Apple and FBI is anything but fantasy, and it concerns the rectangle sitting in your pocket.
Anyone who has attempted to guess an iPhone password knows of the increasing time limits imposed with every wrong input. So what happens when the FBI comes across the iPhone of a confirmed terrorist such as Syed Rizwan Farook, the shooter suspect of last year’s San Bernardino attack, and can’t open it?
They ask for help. Specifically, the FBI has issued a search warrant to Apple requiring them to assist in retrieving data that may still be on the phone. However it isn’t all that simple, and the implications are heavy.
What the government wants
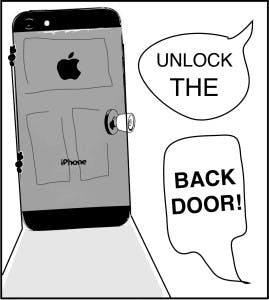
This case goes far beyond simply unlocking a single phone. The FBI is requesting that Apple create a “backdoor” operating system, which they hope to use to force their way into the phone and the data within.
This might seem fairly innocuous, but the repercussions could be widespread. Even if the system is developed to only work on one iPhone, the worry is that the government will reverse-engineer their own version that will work on any phone.
But even beyond this case is what is at stake for potential legal precedent. Should Apple cave and comply with the government order, this may pave the way for the government to require all cell phone manufacturers to implement backdoors into its products.
This is a dangerous thought. With news of the National Security Agency swirling around in recent years, surveillance of the American people has become a hot-button topic, and one that many oppose. To allow the FBI a tool like this would make the transition to mandatory surveillance software all too easy, allowing them to view your messages, photos and location data.
A precedent like this would be a major blow to technology privacy, and should be resisted at all costs. There is something to be said about cooperating with the government when it comes to learning more about terrorists, but when we jeopardize our own security in the process we do ourselves a huge disservice. ,
What Apple can do
Apple has drawn a line in the sand on the issue. While the technology giant has helped the government access phone data before, the recent customer letter put out by CEO Tim Cook claims the FBI has gone too far in its quest for the data on the iPhone.
“The government is asking Apple to hack our own users and undermine decades of security advancements that protect our customers — including tens of millions of American citizens — from sophisticated hackers and cybercriminals,” Cook said in the letter.
According to its statement, Apple intends to oppose the order and challenge the warrant. This is a necessary step, and should be wholeheartedly supported. Apple is looking at the future ramifications of this “one-time” action and taking a stand that they will not begin on the slippery slope to creating surveillance software.
It is still yet to be seen if Apple’s actions will be successful, but opposing a government overreach like this is an admirable step in the right direction. Hopefully other phone manufacturers will follow in Apple's footsteps in the coming years.
What's next
And so, this all winds its way back to your pocket. You’d be hard-pressed to find a classroom on Western’s campus that isn’t populated with Apple phones, and even harder to find would be someone who wants the FBI rifling through their phone.
While there is little beyond support we can offer Apple as it proceeds, there are steps we can take to secure own own data. Using a strong password that is six to seven characters long and uses numbers and letters makes it much harder for anyone to force their way into your phone.
Apple is treading new ground here, and the outcome will determine just how far the government can reach into your phone. The legal precedent that could come from Apple’s cooperation would set our privacy at future risk, and their challenge is the correct thing to do. Our privacy is not something we should negotiate with.